
4GB Apricorn SecureKey USB-C Flash Drive by Apricorn
- Be the first to review
- Item Number: 338-0019
- Part Number: ASK3-NXC-4GB
Key Features
- 4GB flash drive
- Read speed up to 77MB/s
- Write speed up to 72MB/s
- Backed by a 3 years manufacturers warranty
See product description
-
 16GB Star Wars TLJ 1st Order BB Unit USB Flash Drive
16GB Star Wars TLJ 1st Order BB Unit USB Flash Drive
IN STOCK
MP 2750 -
 16GB Guardians of the Galaxy Star Lord USB Flash Drive
16GB Guardians of the Galaxy Star Lord USB Flash Drive
IN STOCK
$ 13.56 -
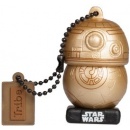 16GB Star Wars TLJ BB-8 Gold USB Flash Drive
16GB Star Wars TLJ BB-8 Gold USB Flash Drive
IN STOCK
$ 18.39 -
 128GB Kingston Technology IronKey Vault Privacy 50 USB3.2 Type-A Flash Drive - Blue
128GB Kingston Technology IronKey Vault Privacy 50 USB3.2 Type-A Flash Drive - Blue
IN STOCK
$ 147.30 -
 128GB SanDisk Ultra Flair Flash USB3.0 Flash Drive - Black,Silver
128GB SanDisk Ultra Flair Flash USB3.0 Flash Drive - Black,Silver
IN STOCK
$ 34.36 -
 256GB AData UC310 USB 3.2 Flash Drive - Black Capless Swivel
256GB AData UC310 USB 3.2 Flash Drive - Black Capless Swivel
IN STOCK
$ 21.09 -
 512GB Transcend JetFlash 930C 2-In-1 USB3.2 Flash Drive
512GB Transcend JetFlash 930C 2-In-1 USB3.2 Flash Drive
IN STOCK
$ 121.99 -
 32GB Harry Potter Lord Voldemort USB Flash Drive
32GB Harry Potter Lord Voldemort USB Flash Drive
IN STOCK
$ 18.39 -
 120GB Apricorn Aegis Secure Key USB3.2 Type A Flash Drive
120GB Apricorn Aegis Secure Key USB3.2 Type A Flash Drive
IN STOCK
$ 231.50 -
 256GB Kingston Technology DataTraveler Max USB3.2 Type-A Flash Drive - Red
256GB Kingston Technology DataTraveler Max USB3.2 Type-A Flash Drive - Red
IN STOCK
$ 50.50 -
 64GB Kingston Technology IronKey Locker+ 50 USB3.2 Type-A Flash Drive - Silver
64GB Kingston Technology IronKey Locker+ 50 USB3.2 Type-A Flash Drive - Silver
IN STOCK
$ 77.36 -
 64GB Kingston DataTraveler microDuo 3C USB-A + USB-C Interfaces USB3.0
64GB Kingston DataTraveler microDuo 3C USB-A + USB-C Interfaces USB3.0
IN STOCK
$ 23.64 -
 16GB Verbatim V3 (3-Pack) USB Flash Drive
16GB Verbatim V3 (3-Pack) USB Flash Drive
IN STOCK
$ 30.46 -
 16GB Apricorn SecureKey 3NXC USB Type C Flash Drive
16GB Apricorn SecureKey 3NXC USB Type C Flash Drive
IN STOCK
$ 109.59 -
 128GB SanDisk Cruzer Blade USB2.0 Flash Drive - Black, Red
128GB SanDisk Cruzer Blade USB2.0 Flash Drive - Black, Red
IN STOCK
$ 18.76
Keep data safe with the 4GB Aegis Secure Key 3NXC Encrypted USB Type-C Flash Drive from Apricorn. Designed for use in data-sensitive environments, this USB 3.2 Gen 1 Type-C encrypted flash drive uses the same cryptography standard as the federal government.
Using hardware-based encryption, this flash drive incorporates brute force defenses, as well as an unattended auto lock feature and a self-destruct PIN. Featuring separate user and admin roles and two read-only modes, this drive is easy to deploy thanks to setup software, programmable PIN lengths, and a drive reset feature.
Built to handle adverse conditions, the Aegis Secure Key is IP68 dust and water resistant, while the extruded aluminum body is crush resistant. Furthermore, the tamper-evident design prevents the drive from being physically compromised. An internal battery allows users to enter their PIN on the wear-resistant keypad before plugging it in, at which point the drive automatically switches over to bus power. This device is compatible with Windows, Mac, Linux, Android, Symbian, and any powered USB OS with a storage file system.
Tough Protection
Software-free, this drive features 100% hardware-based 256-bit AES XTS encryption, onboard keypad PIN authentication, and high-speed USB 3.2 Gen 1 data transfer speeds. All data is encrypted on the fly and the device's PINs and data remain encrypted while the drive is at rest.
Cross-platform compatible and OS agnostic, the Aegis Secure Key is compatible with Windows, Linux, Mac, Android, Chrome, embedded systems, and equipment possessing a powered USB port and storage file system. All internal components are protected from physical tampering with a layer of hardened epoxy, and locked-down firmware brings immunity to malware attacks such as BadUSB.
Aegis Configurator Compatible
This Windows-based app allows for the quick setup of multiple devices at once. Create custom profiles and mass-configure multiple devices in a matter of seconds.
Separate Admin and User Modes
The Aegis Secure Key supports independent Admin and User PINs. The Admin mode controls the universal programmable settings of the device and can only be accessed with the Admin PIN. The User mode is limited to basic external drive functions like read /write, unlock / lock, etc. The data on the drive can also be accessed with the Admin PIN in the User mode.
Polymer-Coated, Wear-Resistant Keypad
Unlocked by entering a PIN on the keypad, this drive does not rely on the host computer's keyboard. Until the device is unlocked via its keypad, it remains invisible to the host. The embedded keypad circumvents hardware- and software-based key-logging attempts to capture passwords by excluding the host system from the authentication process. Polymer-coated buttons are wear-resistant and designed to not reveal commonly used buttons.
Admin Forced Enrollment
Out of the box, there are no factory pre-set default PINs. In order to set up and use the drive, a unique PIN must first be established by the Admin, from within the Admin mode.
User Forced Enrollment
Once a device is configured by the Admin, it can then be deployed in a state in which the User must first establish his or her own User PIN before the drive can be accessed or used.
Data Recovery PINs
In the event that a User PIN is forgotten, Recovery PINs can be programmed into the device to permit access to the drive's data by creating a new state of User Forced Enrollment while the Admin PIN and the drive's data remain intact. Once a replacement User PIN is generated, access to the drive and its contents is restored to the user.
Two Read-Only Modes
These modes can be employed in situations that require the drive's contents to be kept intact and unaltered for later examination. A universal read-only mode is set by the admin from within the admin mode and can't be modified or disabled by anyone but the admin, while a second read-only mode can be set and disabled by a user but can also be enabled or disabled by the admin as well.
Programmable PIN Lengths
Designated by the Admin, PIN lengths can feature a minimum of 7 or maximum of 16 characters. The longer the PIN, the more secure the data on the device becomes. For example, the odds of brute force success go from 1 in 10 million with a 7-digit PIN to 1 in 100 million with an 8-digit PIN. In cases where the User sets up his or her own PIN from User Forced Enrollment, the Admin can set an enhanced User password length requirement as part of the overall security policy.
Brute Force Defense
All Aegis Secure Drives are unlocked or authenticated by entering a PIN on their own onboard keypad. Since the PIN is not entered using the host computer's keyboard, they are not vulnerable to software or hardware-based key-loggers or software-based brute force attacks. However, if the device comes under a physical brute force attack, your data is protected with a programmable brute force hack defense mechanism.
Users can program the drive to crypto-erase after a designated number of failed attempts, ranging from 4 to 20 attempts. If the programmed number of consecutive incorrect password entries has been attempted, the device will delete its own encryption key and destroy the ability to access its stored data.
PIN Guard
The PIN Guard detects inadvertent button presses and puts the device back into sleep mode to prevent battery drainage and false brute force attempt tallies.
Fixed Disk or Removable Media
Easily adapt the drive to embedded equipment and operating systems that will only recognize a Fixed Disk or Removable Media for removable storage. Windows, Mac, and Linux all deal with mass storage devices differently depending on whether they report themselves to the host as Removable Media or as Fixed Disks. Some applications or embedded systems may allow one type but not the other.
Unattended Auto Lock
All Aegis Secure Drives will automatically lock once disconnected from a computer's USB port or the power to that USB port is interrupted, or after a preprogrammed period of inactivity.
Lock Override
Designated for specific cases in which the key needs to remain unlocked through USB port re-enumeration, the lock override allows for use during reboot or with a virtual machine.
Drive Reset
Drive Reset clears both the User and Admin PINs, destroys the data, creates a new randomly generated encryption key, and allows the drive to be reused repeatedly, with an infinite number of randomly generated encryption keys, allowing the admin and or user to reset the drive as often as needed.
Self-Destruct PIN
The last line of defense for data security when the device's physical security is at risk, the self-destruct PIN defends against these physically compromising situations by erasing the key's contents, leaving it in normal working order and appearing as though it is yet to be deployed.
| CAPACITY | 4GB |
| INTERFACE TYPE | USB3.2 Type-C |
| TRANSFER RATES | Read speed up to 77MB/s Write speed up to 72MB/s |
| COLOUR | Black |
| WARRANTY | 3 years manufacturers warranty |